
OR

Information technology has changed the administration, as IT is now an integral part of government-funded agencies, and public and private firms. But IT poses new challenges for data centers and payment gateways in terms of protecting data from unauthorized access, securing electronic transactions, and managing outsourcing services.
A business happens through interdependency to transform resources into results, with the ultimate objective of revenue maximization or cost cutting. Proper IT adoption and automation of business functions help them achieve this goal. But Nepal is technically challenged in terms of cyber and systems security due to high level of dependency on IT services. We need to ensure we can protect our critical infrastructures and respond to attacks from intruders on our own.
There is a need of a paradigm shift in our education system. IT must be its integral part. There are many universities and colleges offering IT courses in Nepal. But is there a match between the syllabus, the competence of the learners, and the requirements of the firms? The government has no clear roadmap on this. But this is by no means solely government business.
Hacking of private and public sites has also become common in Nepal. To protect against hackers there must be a dedicated “ethical hacker” for every sizable organization. Yet the need for such cyber experts is almost entirely ignored in our context. Digitized information is more likely to get breached with no robust systems to protect it. We have been digitizing rapidly but not developing required human and knowledge capital in the sector. Is this not the responsibility of our intellectuals, universities, and colleges?
New service delivery channels such as networked ATMs, internet banking, and mobile banking have increased the risk of electronic fraud. Technology risk is not only concerned with operation risks; attenuated and altered information to mangers also result in poor decisions. Reputation risks have also emerged, again owing to poor IT infrastructure.
Cloud computing can help build brands and enhance service delivery, and reach customers in no time. But accidents are common in high speed with poor roadways. Today, IT can create risks that can put an organization’s reputation on the line and end up destroying critical assets. To reduce these risks, the top management has to understand and strategize the importance of developing and implementing a foolproof cloud computing environment.
The government has understandably felt the need to regulate and guide IT related activities in cyber networks to enable internet service providers (ISP) to tackle emerging cyber frauds and reduce the risks from implementation of information technology. But is the IT industry in Nepal up to the challenge?
There is a need for rigorous research and preparedness in network security assessment to determine vulnerabilities and mitigate associated risks. An anticipatory assessment will help organizations ascertain and mitigate information security threats before they are exploited by malicious software, which in turn might result in financial or reputational loss.
Lack of awareness on cyber intrusions and cyber invasion in business firms is a major concern today. Yet, instead of coordination, there remains a huge gap between government and private players when it comes to securing computer-based transactions, and no effective measure to implement cyber policies and security measures to protect data. Instead, organizations are almost exclusively dependent on internet service providers and foreign systems and software vendors for security. The industry lacks professional IT experts to manage the internet of things.
There is an opportunity for business everywhere and internet enables and accelerates any business’ entry into global markets. But each organization in cloud faces internet security risks and vulnerabilities, no matter what its products and services, and irrespective of its location. As business continually changes, so do technological threats. Awareness among senior management and board members about security loopholes can no longer be delayed. Everyone should realize the importance of internet security. If nothing else, one must better manage the ever-changing risks to create, protect, and enhance stakeholders’ value.
Today no organization has an official post for Chief Risk Officer. The CEO (Chief Executive Officer), or the CFO (Chief Financial Officer) or the CIO (Chief Information Officer) is expected to handle all risks. But this approach is not working. Academic research has found that most organizations in Nepal face great IT risks.
Educational institutions play a vital role in preparing human capital in IT sector. Information techno experts can enable cost efficient, and timely business transaction processing. Any downtime caused by disruption in the underlying technology or the process can lead to loss of trust among customers and other vital stakeholders. But before a company can manage its risks, it has to know what the risks are. And to understand these risks, it’s important to consider strategic business scenarios and have a proper security management system.
The computer networks of some renowned institutions were hacked a few months back. Yet, instead of developing strong protection measures of their own, most organizations are still exclusively dependent on internet and web-service providers to secure their data and information.
For the government’s part, it’s high time to establish Computer Emergency Response Teams (CERTs). There should also be capacity enhancement interventions targeted at Nepal Police to make them more competent on cybercrime investigations. Attention towards information security management and digital forensics is a must given the state of the insecure Nepali Cloud.
The author heads the BCIS program at Apex College. He can be contacted at suman.dahal@apexcollege.edu.np.
You May Like This

Unleashing Nepal's Digital Future
In Nepal's journey into digital transformation, data centers and cloud services become fundamental and foundational digital infrastructure. Data centers ensure... Read More...

Cabinet meeting held through video conferencing for first time
KATHMANDU, Aug 26: Prime Minister KP Sharma Oli, who is currently in Singapore for his health check-up, convened a cabinet... Read More...

PM’s IT consultant ‘misusing power’ to land big contracts
KATHMANDU, Dec 17: Honorary Information Technology (IT) consultant to Prime Minister KP Oli, Asgar Ali, who is also the chief... Read More...



Just In
- Partly cloudy weather likely in hilly region, other parts of country to remain clear
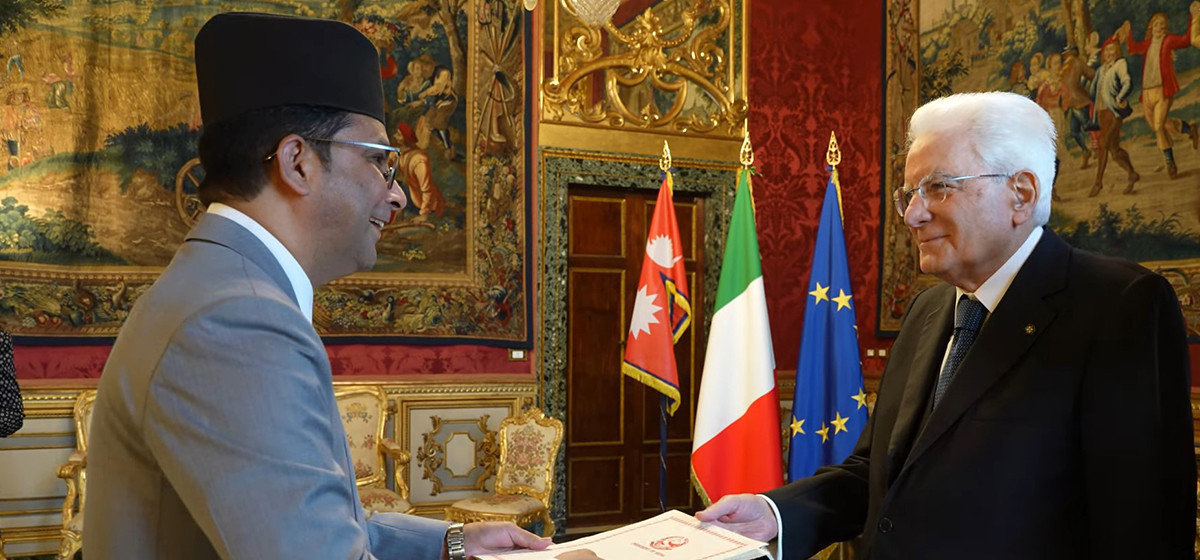
- Nepal’s Non-resident Ambassador to Italy presents Letter of credence to President of Italy
- 104 houses gutted in fire in Matihani (With Photos)
- By-elections: Silence period starts from today, campaigning prohibited
- A Room of One's Own- Creative Writing Workshop for Queer Youth
- Tattva Farms rejuvenates Nepali kitchens with flavored jaggery
- Evidence-Based Policy Making in Nepal: Challenges and the Way Forward
- Insurers stop settling insurance claims after they fail to get subsidies from government













Leave A Comment